PTR records are most commonly used for reverse DNS or mapping an IP address to a domain name. This article focuses on reverse DNS.
PTR records, also called "Pointer Records", are defined in RFC 1035.
DNS Check can monitor your reverse DNS records and notify you if they become unresolvable or start resolving to the wrong domain name. DNS Check also supports monitoring non-reverse-DNS PTR records.
Reverse DNS vs. Forward DNS
Reverse DNS gets its name from the fact that it does the opposite of what A records do for IPv4 and AAAA records do for IPv6.
A and AAAA records are referred to as "forward DNS" records because they map domain names to IP addresses. Reverse DNS (PTR) records, on the other hand, map IP addresses to domain names.
Here's an example of an IPv4 address that has matching forward and reverse DNS:
- The 189.72.131.104.in-addr.arpa PTR record points the 104.131.72.189 IP address to nyc1.dnscheck.co.
- The nyc1.dnscheck.co A record maps to 104.131.72.189.
Here's an example of an IPv6 address that has matching forward and reverse DNS:
- The 1.0.0.b.1.a.7.0.0.0.0.0.0.0.0.0.0.1.0.0.0.0.8.0.0.8.8.a.4.0.6.2.ip6.arpa PTR record points the 2604:a880:800:10::7a1:b001 IP address to nyc1.dnscheck.co.
- The nyc1.dnscheck.co AAAA record maps to 2604:a880:800:10::7a1:b001.
Importance of Reverse DNS
Reverse DNS has special significance when sending email for two reasons:
- It's common for spam filters to check whether the IP address of a server attempting to deliver email matches its forward and reverse DNS records. Servers whose IP addresses lack matching forward and reverse DNS are subject to having their mail deferred, rejected, or sent to the spam folder.
- Matching forward and reverse DNS is a prerequisite for registering for most email feedback loops. Email feedback loops, also sometimes called "complaint feedback loops," are mechanisms ISPs use to share information about spam complaints with email senders. These provide a valuable metric of how "spammy" email is and are used to identify abuse issues.
Reverse DNS Shorthand
As you can see from earlier sections, PTR record names, especially in the IPv6 space, can be unwieldy.
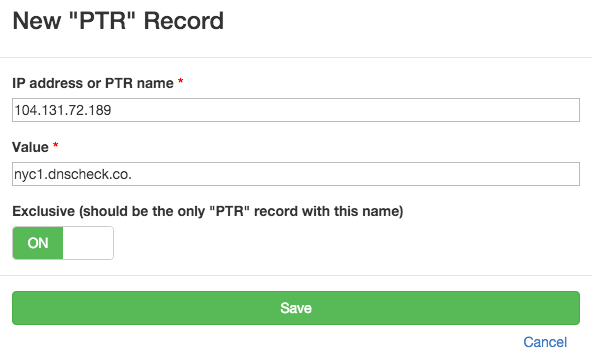
When adding reverse DNS records in DNS Check, you can bypass this complexity by entering the IP address in place of the PTR name. Here's an example:
Alternatively, if you're using the DNS zone file importer, you can use a shorthand to specify matching sets of A and PTR or AAAA and PTR records using this format:
ip-address <=> domainFor example, to import a reverse DNS record for 104.131.72.189 that maps to nyc1.dnscheck.co, and a corresponding A record, enter:
104.131.72.189 <=> nyc1.dnscheck.coTo import a reverse DNS record for 2604:a880:800:10::7a1:b001 that maps to nyc1.dnscheck.co, and a corresponding AAAA record, enter:
2604:a880:800:10::7a1:b001 <=> nyc1.dnscheck.coFields
Here are the fields that make up a PTR record:
| Field | Description | Example |
|---|---|---|
| Name | A fully qualified domain name (FQDN). | 189.72.131.104.in-addr.arpa. |
| Type | The DNS record type. Always set to PTR. | PTR |
| Value | The fully qualified domain name (FQDN) that the PTR record points (resolves) to. | nyc1.dnscheck.co |
DNS Zone File Examples
IPv4 and IPv6 PTR records go in separate zone files.
Here's an example of how an IPv4 PTR record looks in a zone file:
$ORIGIN 72.131.104.in-addr.arpa.
; Name Type Value
189 PTR nyc1.dnscheck.co.
Here's an example of how an IPv6 PTR record looks in a zone file:
$ORIGIN 1.a.7.0.0.0.0.0.0.0.0.0.0.1.0.0.0.0.8.0.0.8.8.a.4.0.6.2.ip6.arpa.
; Name Type Value
b.0.0.1 PTR nyc1.dnscheck.co.
Additional Resources
- RFC 1035 - this RFC defines PTR records. See section 3.5 - "IN-ADDR.ARPA domain" in particular.

Protect your DNS infrastructure with automated monitoring
Get notified immediately when DNS records change. Start monitoring your critical DNS infrastructure for free in under 5 minutes.
No credit card required • Cancel anytime