Monitor CAA Records with DNS Check
DNS Check now supports monitoring CAA records. A CAA record (Certification Authority Authorization record) tells public certificate authorities (CAs) which of them, if any, are allowed to issue TLS/SSL certificates for your domain. Public CAs have been required to honor these records since 2017, so CAA records act as an access control list for certificate issuance.
When your CAA records disappear, change unexpectedly, or pick up an extra entry for a CA you didn't authorize, the consequences range from a 3 a.m. renewal failure to someone else walking off with a valid certificate for your domain. DNS Check now catches those changes and alerts you when they happen.
Why CAA Records Are Worth Monitoring
A domain with no CAA records (and no CAA records on any of its parent domains) can be certified by any public CA. A domain with a single issue record, such as 0 issue "letsencrypt.org", narrows that down to one CA. It's a useful primitive, but only while the record is actually in DNS and still pointing at the CA you mean to use. A few failure modes are worth watching for:
- Accidental removal. A zone edit, a migration, or a botched DNS provider change drops your CAA records. The domain quietly reverts to "any CA can issue," and the protection is gone without anyone noticing.
- Unauthorized additions. A new
issuerecord appears for a CA you don't use. That's the kind of change a security team wants to see immediately. - Parameter drift. If you've used the RFC 8657 parameters to pin issuance to a specific ACME account (
accounturi) or a specific challenge type (validationmethods), a change to either one can widen your attack surface or break a working renewal, without the record looking obviously different at a glance.
DNS Check picks these up the same way it picks up any other DNS change: it polls your authoritative name servers on a schedule and compares each response against the records you've configured.
What DNS Check Supports
CAA monitoring covers the full set of tags defined by RFC 8659 and its follow-ups:
issuefor authorizing a CA to issue certificates for the domain.issuewildto overrideissuespecifically for wildcard certificates.iodeffor the URL or mailto address where issuance violations should be reported.issuemailfor authorizing S/MIME certificate issuance (RFC 9495).issuevmcfor authorizing Verified Mark Certificates used with BIMI.contactemailandcontactphonefor the CA/Browser Forum domain holder contact tags.
The RFC 8657 parameters on issue and issuewild (accounturi and validationmethods) work too, so you can monitor records that pin issuance to a specific ACME account or a particular challenge type:
example.com. CAA 0 issue "letsencrypt.org; accounturi=https://acme-v02.api.letsencrypt.org/acme/acct/12345; validationmethods=dns-01"
Setting Up a CAA Record Check
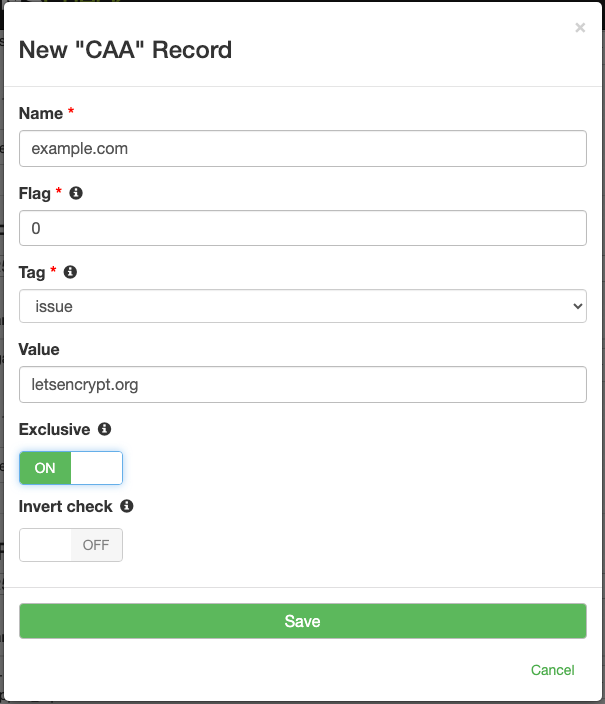
To add a CAA check from the DNS record group page:
- Click "Add DNS record".
- Select "CAA" as the record type.
- Enter the name, flag (almost always 0), tag, and value.
- Save the record.
If you'd rather not click through the form for every record, paste a zone file with your existing CAA records, and DNS Check will import them. The importer accepts any tag name that's valid under RFC 8659, so unusual or vendor-specific tags come through cleanly even when the add-record form doesn't list them in its tag dropdown.
When a CAA record changes, you'll hear about it through your usual notification channels: email, Slack, PagerDuty, webhooks, and the rest.
Available on Every Account
CAA record monitoring is available on every DNS Check account, including free plans. There's no upgrade to buy and nothing to enable. If you've been holding off on adding CAA records because a typo silently breaking a TLS renewal sounds worse than no CAA records at all, monitoring takes most of that risk off the table. DNS Check queries your CAA records every few minutes and alerts you the first time one disappears, changes, or stops resolving. That buys you time to fix things before the next renewal attempt.
For the full reference, including the tag list, flag semantics, and zone file examples, see the CAA record monitoring documentation. If you're new here, create a free DNS Check account and start monitoring your DNS records.