Monitor CAA Records with DNS Check
DNS Check now supports monitoring CAA records. A CAA record (Certification Authority Authorization record) tells public certificate authorities (CAs) which of them, if any, are allowed to issue TLS/SSL certificates for your domain. Public CAs have been required to honor these records since 2017, so CAA records act as an access control list for certificate issuance.
When your CAA records disappear, change unexpectedly, or pick up an extra entry for a CA you didn't authorize, the consequences range from a 3 a.m. renewal failure to someone else walking off with a valid certificate for your domain. DNS Check now catches those changes and alerts you when they happen.
Continue reading Monitor CAA Records with DNS Check »
Dark Mode Has Arrived
It's 2026, and DNS Check now has a dark mode. Yes, we noticed the year. Better late than dazzling our users at 2 a.m. when an MX record decides to misbehave.
The 2 a.m. Use Case
If you've ever been paged for a DNS issue, you know the routine: the alert fires, you open your laptop, and your monitoring dashboard greets you with a screen full of white. Dark mode is a small quality-of-life improvement that you don't think much about during the day and are very glad for at 2 a.m.
Continue reading Dark Mode Has Arrived »
New Features: Team Members and Additional Email Recipients
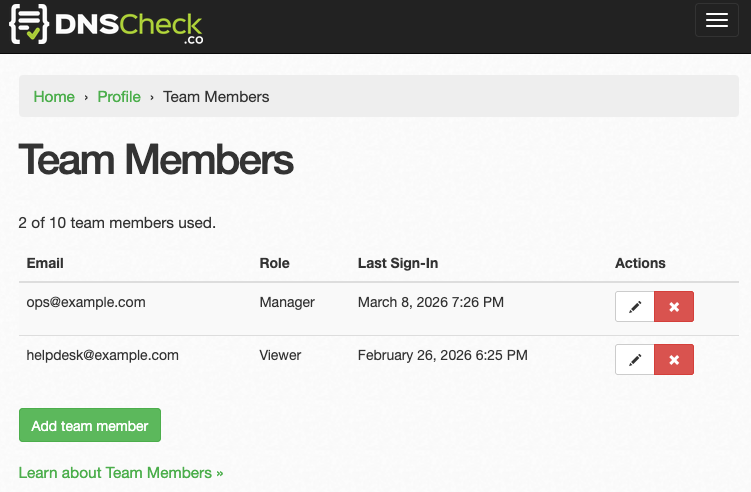
DNS Check now supports two features for Enterprise accounts that make it easier to work as a team: Team Members and Additional Email Recipients. Team Members lets multiple people log in and work with your DNS records using their own credentials. Additional Email Recipients sends notification emails to people who need to stay informed but don't need to log in.
Continue reading New Features: Team Members and Additional Email Recipients »
Monitor Load Balanced DNS Records with CIDR Ranges
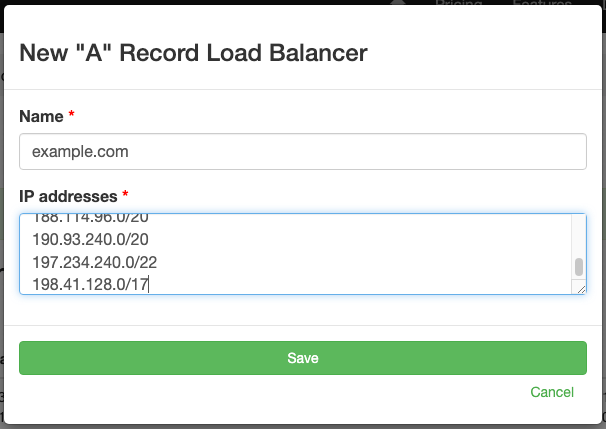
DNS Check's load balancer monitoring now supports CIDR notation, making it practical to monitor domains served by CDNs and cloud providers that use large IP pools. Instead of listing every possible IP address a provider might return, you can enter CIDR ranges like 104.16.0.0/13 and DNS Check will verify that responses fall within those ranges.
Continue reading Monitor Load Balanced DNS Records with CIDR Ranges »
Guided DNS Troubleshooting, Full History, and UI Improvements
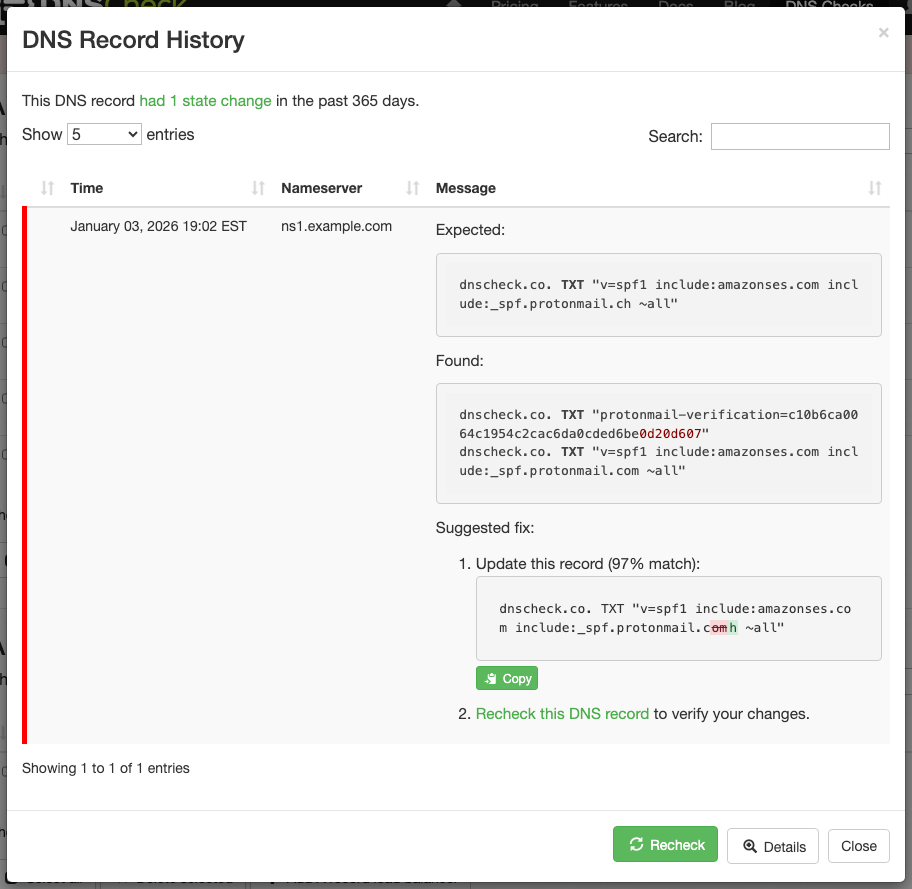
We're kicking off 2026 by shipping improvements that make DNS troubleshooting faster and more intuitive. When a DNS check fails, you'll now see exactly what needs to change to fix it, and you'll have complete visibility into your DNS record behavior over time.
Suggested Fix Report
When a DNS record check fails, the new Suggested fix report shows exactly what action you need to take. Instead of manually comparing "Expected" vs "Found" records character-by-character, DNS Check now performs that comparison for you and presents clear guidance.
Continue reading Guided DNS Troubleshooting, Full History, and UI Improvements »
Detect DNS Record Creation: Planned or Rogue
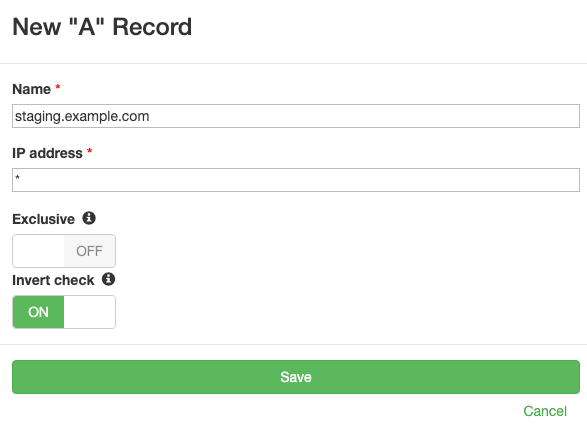
We're excited to announce one of our most frequently requested features: inverted DNS checks. This new capability allows you to detect when DNS records are created (whether they're planned infrastructure changes or rogue records) and prevent unwanted values from appearing in your DNS configuration.
Understanding Inverted Checks
Traditional DNS monitoring follows straightforward logic: the check passes when your DNS records match the expected configuration. An A record check for example.com pointing to 192.0.2.100 passes when DNS queries return that specific IP address and fails when the record is absent or returns a different value.
Inverted checks reverse this logic. When you enable the "Invert check" option, the check passes when the DNS record is not found or when it exists with a value that differs from the specified value. This inverted logic addresses common operational scenarios that traditional monitoring systems can't handle.
Continue reading Detect DNS Record Creation: Planned or Rogue »
Amazon Isn't Eating Its Own DNS Dog Food
Updated October 24, 2025: Added TL;DR per reader feedback for clarity.
TL;DR
The evidence shows that:
- amazon.com uses name servers (amzndns.*) hosted by Vercara, LLC (UltraDNS)
- aws.com and aws.amazon.com use name servers (awsdns.*) hosted by Amazon.com, Inc. (Route 53)
On October 19-20, 2025, Amazon Web Services (AWS) experienced a significant outage (AWS status) affecting its US-EAST-1 region in northern Virginia. The root cause was DNS resolution failures for DynamoDB's API endpoints, which cascaded across AWS's interconnected services, disrupting major platforms including Snapchat, McDonald's, Disney+, Roblox, Coinbase, Reddit, and Amazon's own services.
While investigating the outage, I discovered that Amazon doesn't use its own AWS Route 53 service for amazon.com's DNS.
Eating Your Own Dog Food
"Eating your own dog food" (or "dogfooding") is a practice where a company uses its own products or services internally. The phrase originated in the 1980s in the technology industry, and it serves several important purposes:
- Quality assurance: Internal usage exposes bugs and usability issues before customers encounter them
- Credibility: Demonstrating confidence in your own products builds customer trust
- Employee understanding: Teams gain firsthand experience with what they're building and selling
Many major technology companies have embraced dogfooding as a core principle. Atlassian uses Jira for all internal development, recently detailing how they dogfood new features like their Rovo Dev coding agent across all internal Jira sites. Slack deploys every new feature to an internal "Dogfood" tier first, where all Slack employees use it before external customers see it, helping catch problems early.
These companies understand that if their products aren't good enough for their own use, they shouldn't be selling them to customers. A company that uses its own products creates a positive feedback loop, making the products even better.
DNS Check follows this same principle. We monitor our own critical DNS records using our service, including dnscheck.co's authoritative name servers, MX records, and TXT records. When we add new features or make infrastructure changes, we experience the same monitoring alerts, notification workflows, and diagnostic tools that our customers use. This internal usage helps us identify potential improvements and ensures we're building features that genuinely matter for DNS monitoring.
Continue reading Amazon Isn't Eating Its Own DNS Dog Food »
Lessons from the October 2025 AWS DNS Outage
Early on October 20, 2025, Amazon Web Services (AWS) experienced a significant outage affecting its US-EAST-1 region in northern Virginia. The root cause was DNS resolution failures for DynamoDB's API endpoints, which cascaded across AWS's interconnected services. The incident disrupted major platforms including Signal, Snapchat, Fortnite, Reddit, Coinbase, Ring, Amazon's own Alexa and Prime Video services, and banking applications for institutions like Bank of Scotland, Halifax, and Lloyds.
This outage demonstrates a fundamental truth about modern cloud infrastructure: DNS failures create disproportionate impact. When DNS resolution fails, even perfectly healthy servers become unreachable, effectively taking services offline.
Timeline and Technical Details
AWS first reported elevated error rates across multiple services at approximately 3:11 AM ET. The company identified the root cause as DNS resolution issues affecting DynamoDB API endpoints in the US-EAST-1 region. DynamoDB serves as a foundational service for many AWS offerings, so DNS failures preventing applications from resolving DynamoDB endpoints created cascading failures across more than 70 AWS services.
By 6:35 AM ET, AWS reported that the DNS issue had been "fully mitigated" and service operations were returning to normal. However, some services experienced lingering effects as backlogs cleared and systems recovered. The total disruption lasted approximately 3-4 hours for most affected services.
The incident highlights how DNS is a critical dependency of distributed systems. When DNS resolution fails, services can't locate the API endpoints they depend on. This creates the same observable failure as if those endpoints were completely offline, even though the underlying infrastructure might be functioning normally.
Continue reading Lessons from the October 2025 AWS DNS Outage »
Performance and Reliability Enhancements
Over the past few months, we've heard from DNS Check customers encountering increasingly complex DNS configurations. Modern domains often accumulate dozens of TXT records for email authentication, domain verification, and security tokens, creating responses that exceed traditional UDP limits and trigger complex fallback mechanisms. These scenarios were generating confusing error messages and, in some cases, false alerts when DNS servers didn't handle large responses correctly.
We're excited to announce significant performance and reliability enhancements that directly address these challenges. These improvements make DNS troubleshooting clearer, reduce false alerts, and ensure accurate monitoring of your critical DNS records, regardless of how complex your DNS configuration becomes.
Enhanced DNS Error Diagnostics
Continue reading Performance and Reliability Enhancements »
Two New DNS Record Monitoring Features
We're excited to announce two significant enhancements to DNS Check: DNS Record Flapping Detection and Extended Notification History. These features streamline the troubleshooting process for recurring DNS resolution errors and reduce repetitive notifications.
DNS Record Flapping Detection
DNS record flapping occurs when a record rapidly alternates between passing and failing states. With our new feature, DNS Check identifies records that change state six or more times within two hours as flapping. This proactive detection serves two primary purposes:
Continue reading Two New DNS Record Monitoring Features »
Subscribe via RSS

