Announcing DNS Check / Basecamp 3 Integration
We're excited to announce that we've integrated DNS Check with Basecamp 3. This integration enables you to receive notifications in the Basecamp Campfire chat of your choice each time a DNS record transitions between passing and failing:
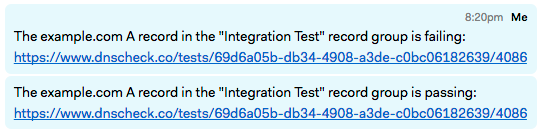
Integrating your DNS Check account with Basecamp 3 is simple, and only takes about a minute. See the DNS Check / Basecamp 3 integration Guide to get started.
Continue reading Announcing DNS Check / Basecamp 3 Integration »
DNS CNAME Load Balancer Monitoring
We've added CNAME DNS load balancer monitoring to DNS Check.
DNS load balancers distribute load for performance and/or redundancy purposes.
You can also use DNS Check to monitor A record and AAAA record based load balancers:
Continue reading DNS CNAME Load Balancer Monitoring »
SPF Record Monitoring
We've added SPF resource record monitoring to DNS Check.
SPF records are used to control which IP addresses and services are authorized to send email for a domain name.
SPF records are unusual in that they can actually be published using either of the following resource record types:
Continue reading SPF Record Monitoring »
Internationalized Domain Name (IDN) Monitoring with DNS Check and Punycode
We've added support for monitoring Internationalized Domain Names (IDNs) using DNS Check.
The DNS protocol uses ASCII characters to represent domain names. That works fine for domains which only contain English alphabet characters, but leaves many other languages short-changed.
Internationalized Domain Names (IDN) address this shortcoming by encoding non-ASCII characters. Punycode is used to encode Unicode characters into ASCII representations. For example, domaiñ.com contains a non-ASCII ñ character, so Punycode translates it to xn--domai-sta.com.
Continue reading Internationalized Domain Name (IDN) Monitoring with DNS Check and Punycode »
DNS Load Balancer Monitoring
We've added DNS load balancer monitoring to DNS Check.
DNS load balancers are used to distribute load for performance and/or redundancy purposes.
You can use DNS Check to monitor both A record and AAAA record based load balancers:
Continue reading DNS Load Balancer Monitoring »
Check Multiple DNS Name Servers
Paid DNS Check accounts have the ability to monitor custom name servers. Up to this point, each DNS record group has been limited to a single custom name server. This has meant that if you wanted to monitor multiple name servers, you would have to create a DNS record group for each.
Today we've increased the number of custom name servers that a DNS record group can have from 1 to 10.
What should a DNS monitoring service do when it's configured to check multiple name servers, and provide a single pass/fail result? Here's what we came up with:
Continue reading Check Multiple DNS Name Servers »
DNS ServFail Errors
DNS record lookups can fail for a number of reasons, the most common of which is due what's called a "ServFail" error.
ServFail errors occur when there's an error communicating with a DNS server. This could have a number of causes, including an error on the DNS server itself, or a temporary networking issue.
Fortunately, most domains use multiple authoritative DNS servers, so if there is a short-lived ServFail issue on one name server which doesn't impact the others, DNS lookups should still work. That said, if a name server has chronic ServFail issues, we recommend investigating why. ServFail errors happen, but should be rare.
Continue reading DNS ServFail Errors »
ALIAS and ANAME Record Monitoring
We've added ALIAS record monitoring to DNS Check.
An ALIAS record maps one DNS record to another of the same type. For example, you might use an ALIAS record to make the widgets.com A record resolve to the same IP address as the www.widgets.com A record:
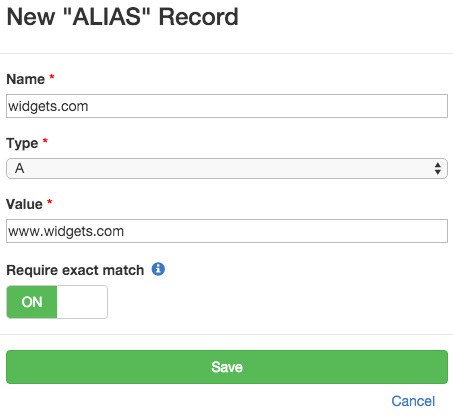
ALIAS records have some similar use cases to CNAME records, with a few important differences:
Continue reading ALIAS and ANAME Record Monitoring »
How to Monitor Multiple DNS Records with the Same Name and DNS Record Type
DNS is incredibly flexible. One of the things that it allows you to do is enable load balancing and/or redundancy by creating multiple DNS records with the same name and record type. For example, you could create two A records for your company's domain name to perform round robin load balancing between two web servers. Another example is creating multiple MX records, so that failure of a single mail server doesn't take incoming email offline.
Unfortunately, this capability increases the complexity of monitoring DNS records, even if you're not intentionally using it. Having an extra, invalid DNS record could cause impaired performance, a service outage, or enable a man in the middle attack.
Today we're proud to announce an improvement to DNS Check which simplifies monitoring for these types of DNS issues.
The "Exclusive" Option
Each DNS record that's monitored by DNS Check has an "Exclusive" option which you can turn on and off:
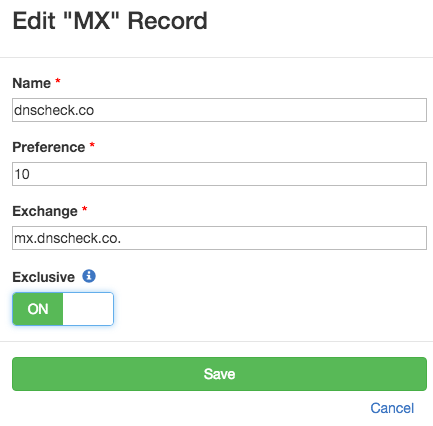
When this option is turned on, DNS Check compares the full list of DNS records returned to the list of DNS records being monitored for the given record name / type combination. If the two sets of records match up exactly, the check passes. Otherwise, DNS Check will detect the error, and notify you about it.
This is an enhancement to DNS Check's previous functionality. The "Exclusive" option was initially released in May 2015, but was limited verifying that only one DNS record existed for a given name / type combination. Today's release removes the single record limitation. You can now specify that multiple "Exclusive" records should exist for the same name / type combination.
When the "Exclusive" option is turned off, DNS Check simply verifies that a DNS record exists with the value specified. It does not report any kind of error if additional records are returned.
We recommend turning the "Exclusive" option on whenever possible.
Continue reading How to Monitor Multiple DNS Records with the Same Name and DNS Record Type »
New Enterprise Tier Added to DNS Check
In April 2015 we launched DNS Check as a free service that allows you to monitor up to 10 DNS records for free, and get notified if any of them stop (or start) resolving to the values that you expect them to. This free service is now our "Basic" account type, and is still our most popular offering.
In May we added a paid tier which checks up to 100 DNS records at a time, and adds the ability to query custom name servers. This is known as our "Professional" account type.
Today we're proud to announce that we've added a new "Enterprise" account type to DNS Check. Enterprise accounts monitor up to 1,000 DNS records.
Continue reading New Enterprise Tier Added to DNS Check »
Subscribe via RSS